ALAN ZISMAN ON TECHNOLOGY
Meeting Android malware face to face 17 January 2013
by Alan Zisman (c) 2013
In the 1980s and 90s, Apple went head to head with Microsoft; by about 1995, Windows was on over 95% of the world’s personal computers and Apple was – temporarily as it turned out – on the ropes.
The last couple of years could be seen as a sort of replay, replacing personal computers with mobile systems – smartphones and tablets – and replacing Microsoft with Google. This time around, we have Apple offering up its iOS operating system, only available on Apple-branded iPhones and iPads and Google with its Android operating system, available on phones and tablets from a wide range of manufacturers. Last stats I’ve seen has Apple maintaining a sales lead in the US, while Android is on the majority of smartphones (etc) sold world-wide.
It’s not an exact analogy - but just as Windows became the target of choice for personal computing malware, the same thing seems to be happening to Android. Security company Sophos has called Android ‘Today’s Biggest Target.’ Some of this is simply opportunity – while Apple keeps a tight grip on the apps that appear on the iOS App Store, Google has made it easy to post apps on its equivalent Play Store (formerly Android Market.) (An aside – what an awful name!)
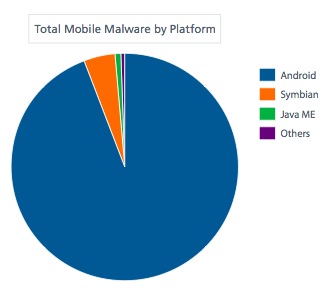
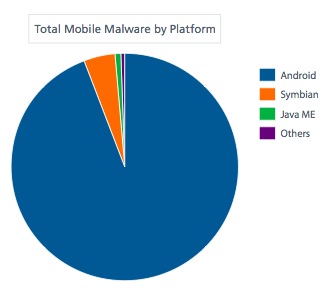
In its Q3 2012 Threats Report, security firm McAfee noted ‘The Android platform remains the largest target for both mobile malware and spyware. In fact, we see very few mobile threats that are not directed at Android phones. After a slight decline earlier in the year, Android malware has rebounded and almost doubled this quarter compared with the second quarter.’ (The graph is from Mcafee's report.)
 And
while iPhone and iPad users are most likely to expose their devices to
malware if they’ve bypassed Apple’s controls by ‘jailbreaking’, Android
users don’t need to ‘root’ their phones or tablets – the equivalent of
jailbreaking them. They simply need to download and install the wrong
apps from Google’s Play Store. And Android users can download and
install apps from other app stores (Amazon’s is popular, for instance)
and even from direct downloads or links in email messages, making it
even harder for Google to have any semblance of control. On January 19 2013, the BBC reported that 1 million Chinese Android users were infected by a Trojan found on over 7,000 apps downloaded from non-Google app stores.
And
while iPhone and iPad users are most likely to expose their devices to
malware if they’ve bypassed Apple’s controls by ‘jailbreaking’, Android
users don’t need to ‘root’ their phones or tablets – the equivalent of
jailbreaking them. They simply need to download and install the wrong
apps from Google’s Play Store. And Android users can download and
install apps from other app stores (Amazon’s is popular, for instance)
and even from direct downloads or links in email messages, making it
even harder for Google to have any semblance of control. On January 19 2013, the BBC reported that 1 million Chinese Android users were infected by a Trojan found on over 7,000 apps downloaded from non-Google app stores.
And it’s not just by looking for porn or pirate copies of movies and TV shows. Late in 2012, for instance, Android users were warned about malicious games in the Play Store.
Early in 2012, Google announced it was going to get tough on Android security and was going to scan apps uploaded to the Play Store. Unfortunately, it hasn’t worked out that way – one report suggests that Google’s app verification service identified only 15% of malware samples sent it by the Android Malware Genome Project In October, TrustGo reported that ‘high risk’ apps among the Play Store’s Top 500 apps had been downloaded 175 million times.
I routinely install anti-malware software on Android devices – I like the free Sophos Mobile Security.
(Here's a review of three other free Android antivirus alternatives).
 The other day, I was looking for a flashlight app for my Android smartphone. Google’s Play Store reports over 8800 results.
The other day, I was looking for a flashlight app for my Android smartphone. Google’s Play Store reports over 8800 results.
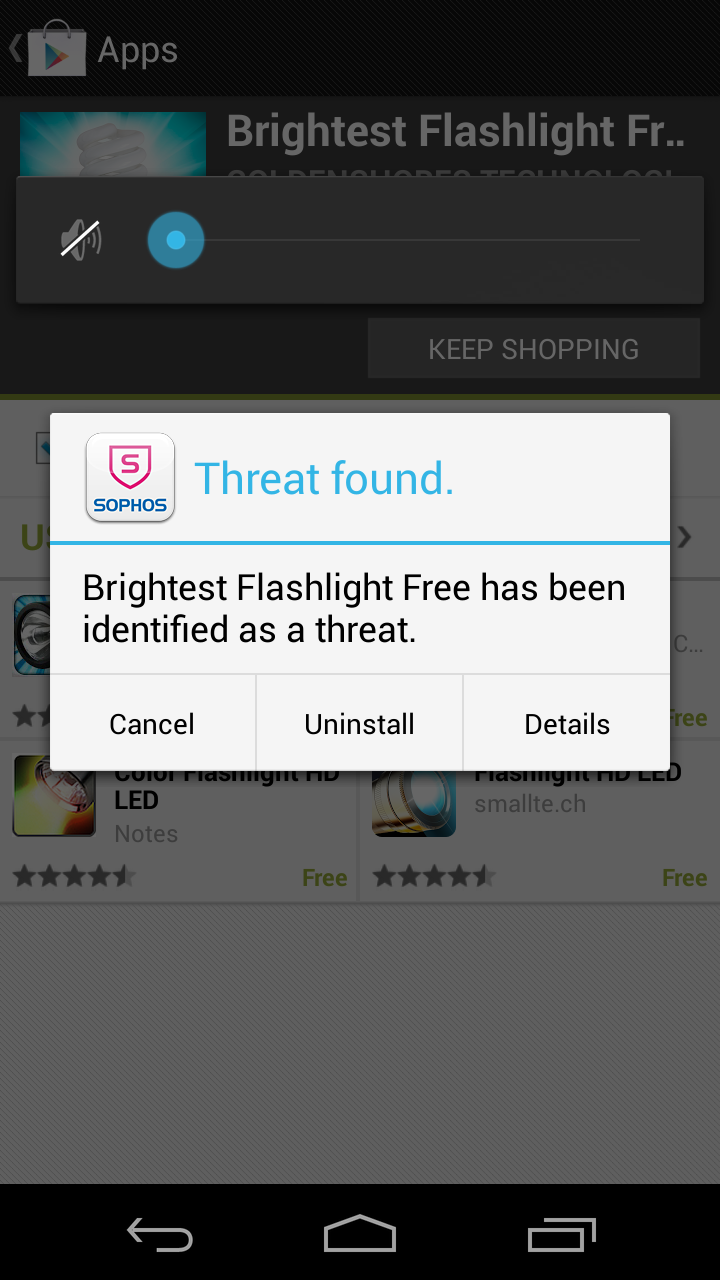
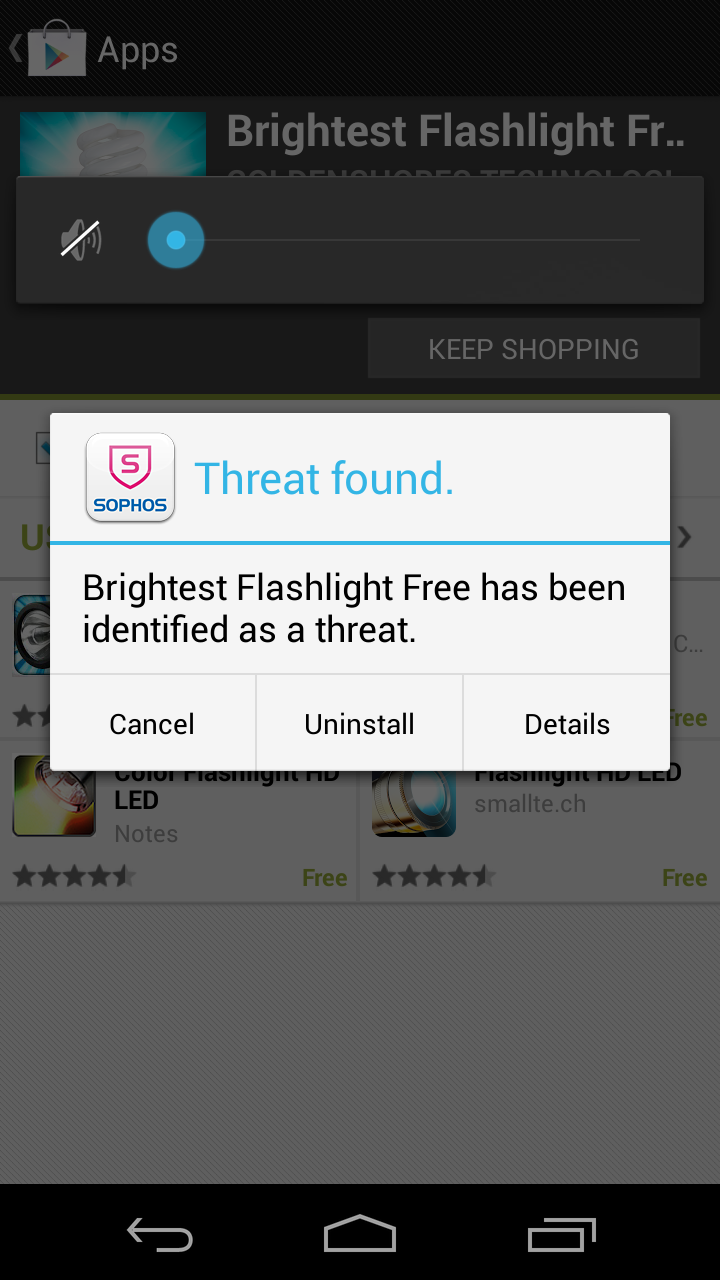
Brightest Flashlight Free is listed high amongst them, and rated 4.8 stars by users. Installing it, however, got a warning message from Sophos – it has been identified as a threat. Sophos goes on to identify it as Threat Andr/NewyearL-B. Apparently, this results in silently making changes to the device such as altering the browser home page.
Perhaps not the nastiest malware imaginable, but I let Sophos automatically uninstall the app, opting instead for the Tiny Flashlight+LED app. Sophos notes that other mobile malware is designed to steal personal identification information used in financial transactions or to send costly premium-rate SMS messages. McAfee’s report discusses Android malware that silently purchases apps from third-party app stores, billing the user.
Brightest Flashlight Free may have worked perfectly well as a smartphone flashlight – other reported Android malware included a fully functioning version of the popular game Angry Birds.
As I’ve said, I recommend that all Android users download and install anti-malware software such as the free Sophos app. Windows users are currently plagued with faux anti-malware software which claims to identify security issues then offers to fix the problem for a price. Sophos recently blogged about Android Armour – a program that appears to by piggy-backing on a legitimate anti-malware program’s scanner, while charging a user $0.99 per week – about $50 a year – for the privilege.
Afterwards - later in January, Trend Micro noted that they've identified 350,000 Android malware - a number that could grow to one million by the end of 2013.
Older blog postings....
Meeting Android malware face to face 17 January 2013
by Alan Zisman (c) 2013
In the 1980s and 90s, Apple went head to head with Microsoft; by about 1995, Windows was on over 95% of the world’s personal computers and Apple was – temporarily as it turned out – on the ropes.
The last couple of years could be seen as a sort of replay, replacing personal computers with mobile systems – smartphones and tablets – and replacing Microsoft with Google. This time around, we have Apple offering up its iOS operating system, only available on Apple-branded iPhones and iPads and Google with its Android operating system, available on phones and tablets from a wide range of manufacturers. Last stats I’ve seen has Apple maintaining a sales lead in the US, while Android is on the majority of smartphones (etc) sold world-wide.
It’s not an exact analogy - but just as Windows became the target of choice for personal computing malware, the same thing seems to be happening to Android. Security company Sophos has called Android ‘Today’s Biggest Target.’ Some of this is simply opportunity – while Apple keeps a tight grip on the apps that appear on the iOS App Store, Google has made it easy to post apps on its equivalent Play Store (formerly Android Market.) (An aside – what an awful name!)
In its Q3 2012 Threats Report, security firm McAfee noted ‘The Android platform remains the largest target for both mobile malware and spyware. In fact, we see very few mobile threats that are not directed at Android phones. After a slight decline earlier in the year, Android malware has rebounded and almost doubled this quarter compared with the second quarter.’ (The graph is from Mcafee's report.)
 And
while iPhone and iPad users are most likely to expose their devices to
malware if they’ve bypassed Apple’s controls by ‘jailbreaking’, Android
users don’t need to ‘root’ their phones or tablets – the equivalent of
jailbreaking them. They simply need to download and install the wrong
apps from Google’s Play Store. And Android users can download and
install apps from other app stores (Amazon’s is popular, for instance)
and even from direct downloads or links in email messages, making it
even harder for Google to have any semblance of control. On January 19 2013, the BBC reported that 1 million Chinese Android users were infected by a Trojan found on over 7,000 apps downloaded from non-Google app stores.
And
while iPhone and iPad users are most likely to expose their devices to
malware if they’ve bypassed Apple’s controls by ‘jailbreaking’, Android
users don’t need to ‘root’ their phones or tablets – the equivalent of
jailbreaking them. They simply need to download and install the wrong
apps from Google’s Play Store. And Android users can download and
install apps from other app stores (Amazon’s is popular, for instance)
and even from direct downloads or links in email messages, making it
even harder for Google to have any semblance of control. On January 19 2013, the BBC reported that 1 million Chinese Android users were infected by a Trojan found on over 7,000 apps downloaded from non-Google app stores.And it’s not just by looking for porn or pirate copies of movies and TV shows. Late in 2012, for instance, Android users were warned about malicious games in the Play Store.
Early in 2012, Google announced it was going to get tough on Android security and was going to scan apps uploaded to the Play Store. Unfortunately, it hasn’t worked out that way – one report suggests that Google’s app verification service identified only 15% of malware samples sent it by the Android Malware Genome Project In October, TrustGo reported that ‘high risk’ apps among the Play Store’s Top 500 apps had been downloaded 175 million times.
I routinely install anti-malware software on Android devices – I like the free Sophos Mobile Security.
(Here's a review of three other free Android antivirus alternatives).
 The other day, I was looking for a flashlight app for my Android smartphone. Google’s Play Store reports over 8800 results.
The other day, I was looking for a flashlight app for my Android smartphone. Google’s Play Store reports over 8800 results.Brightest Flashlight Free is listed high amongst them, and rated 4.8 stars by users. Installing it, however, got a warning message from Sophos – it has been identified as a threat. Sophos goes on to identify it as Threat Andr/NewyearL-B. Apparently, this results in silently making changes to the device such as altering the browser home page.
Perhaps not the nastiest malware imaginable, but I let Sophos automatically uninstall the app, opting instead for the Tiny Flashlight+LED app. Sophos notes that other mobile malware is designed to steal personal identification information used in financial transactions or to send costly premium-rate SMS messages. McAfee’s report discusses Android malware that silently purchases apps from third-party app stores, billing the user.
Brightest Flashlight Free may have worked perfectly well as a smartphone flashlight – other reported Android malware included a fully functioning version of the popular game Angry Birds.
As I’ve said, I recommend that all Android users download and install anti-malware software such as the free Sophos app. Windows users are currently plagued with faux anti-malware software which claims to identify security issues then offers to fix the problem for a price. Sophos recently blogged about Android Armour – a program that appears to by piggy-backing on a legitimate anti-malware program’s scanner, while charging a user $0.99 per week – about $50 a year – for the privilege.
Afterwards - later in January, Trend Micro noted that they've identified 350,000 Android malware - a number that could grow to one million by the end of 2013.
Older blog postings....
| About This Blog... I've been writing about computers, software, Internet and the rest of technology since 1992, including a 17 year (1995-2012) stint as 'High Tech Office' columnist for Business in Vancouver. This blog includes thoughts on technology, society, and anything else that might interest me. Comments, emailed to alan@zisman.ca are welcome - and may be published in whole or part. You can follow me on Twitter for notice of new blog postings. |
 |